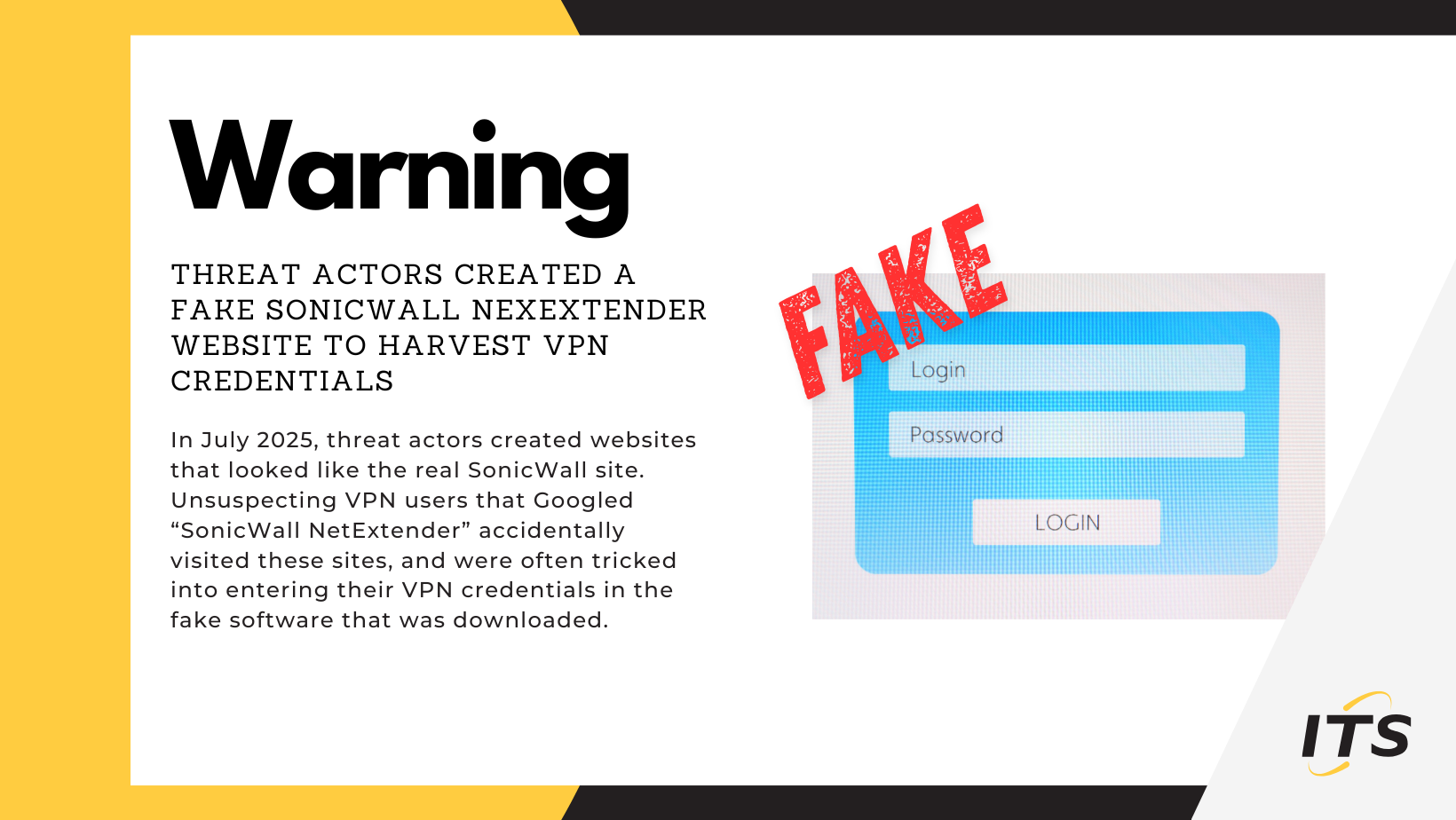
Cybercriminals have created fraudulent websites mimicking SonicWall’s legitimate download page to harvest VPN credentials. Users searching for “SonicWall VPN download” on Google inadvertently landed on these deceptive sites, where entering login information exposed their credentials to attackers.
The Threat
Compromised VPN access enables threat actors to:
- Infiltrate corporate networks remotely
- Deploy malicious software
- Exfiltrate sensitive information
- Disrupt business continuity
How to Protect Yourself
- Navigate directly to official vendor websites using saved bookmarks or accurate URLs
- Avoid relying on search results for software downloads
- Verify website legitimacy by confirming HTTPS protocols and correct domain spelling
- Preview destination links before clicking
- Report suspicious websites to your IT department immediately
Key Takeaway
Always go directly to the source when you need to download an application or file, and take care to double-check the website address. This represents sound security hygiene applicable across all software downloads — not just SonicWall.
If you have concerns about your VPN security, contact our team.